Solid PTC: An Expert Review and Installation Deep Dive - Activated
Solid PTC: An Expert Review and Installation Deep Dive
When evaluating self-hosted solutions for establishing a proprietary pay-per-click (PPC) advertising network, the promise of granular control and tailored functionality is often a primary driver. Platforms offering such capabilities aim to empower operators to bypass third-party dependencies, directly managing advertisers, publishers, and the transaction flow. It's within this niche that software like [Solid PTC - Advanced Pay Per Click Platform](https://gplpal.com/product/solid-ptc-advanced-pay-per-click-platform/) presents itself, claiming to provide a comprehensive framework for precisely this purpose. As senior web developers and technical journalists, our interest lies not in marketing claims, but in the raw technical viability, the operational overhead, and the genuine utility such a system offers under real-world pressure. We dissect its architecture, scrutinize its feature set, and provide a detailed deployment guide, offering an unvarnished perspective on its place in the advertising technology landscape.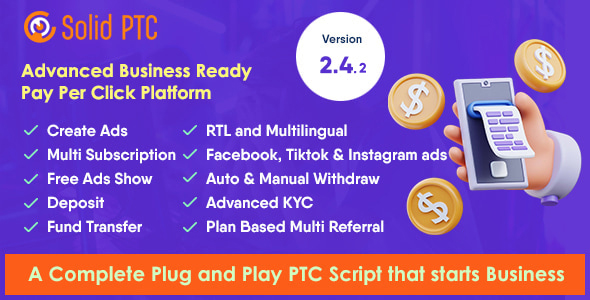
Technical Review: Deconstructing Solid PTC
Architectural Foundation and Core Mechanics
Solid PTC, like many self-hosted advertising platforms, typically operates on a LAMP (Linux, Apache, MySQL, PHP) or LEMP (Linux, Nginx, MySQL, PHP) stack. This is a pragmatic choice, given the widespread availability of hosting environments supporting these technologies. The core of any PTC platform is its ability to manage three distinct user roles: the administrator, the advertiser, and the publisher (or "member").-
Administrator Panel: This is the operational nerve center. It should provide comprehensive tools for user management (registration, suspension, deletion), financial management (deposits, withdrawals, payment gateways, fraud detection), advertisement management (approval, statistics, budgeting), and system configuration (settings, anti-cheat mechanisms, templates). A truly "advanced" platform will offer API access for integration with external systems, robust reporting, and perhaps even multi-language support. The efficiency of this panel directly dictates the operational expenditure for maintaining the network.
-
Advertiser Panel: Here, advertisers should be able to create, manage, and monitor their campaigns. This includes defining ad types (click, banner, text, video, exchange), setting budgets, targeting options (geo-targeting, demographics if collected), and viewing detailed performance analytics (impressions, clicks, CTR, conversions, conversion tracking integration). The user experience for advertisers is paramount; a convoluted interface will deter adoption and reduce ad spend.
-
Publisher/Member Panel: Publishers are the lifeblood, earning revenue by displaying ads or performing tasks. Their panel needs to be intuitive, allowing them to view earnings, request payouts, manage referrals, and access promotional materials. Crucially, it must present clear, real-time statistics on their activity and earnings to foster trust and engagement.
The "Advanced" moniker suggests features beyond basic click tracking. This often implies sophisticated anti-cheat systems (IP/proxy detection, click frequency limits, behavioral analysis, bot traffic identification), diverse payment gateways (PayPal, Payeer, cryptocurrencies, manual bank transfers), multi-level referral systems, and perhaps even integrated content management or gamification elements to boost member engagement. However, the implementation quality of these "advanced" features varies significantly across commercial scripts. Superficial anti-cheat can be easily bypassed by moderately skilled fraudsters, and poorly integrated payment gateways can introduce security vulnerabilities or operational headaches, leading to chargebacks and financial losses. The true "advancement" lies in the robustness and maintainability of these critical components.
Security Posture: A Critical Lens
For any platform handling financial transactions and user data, security is not an optional extra; it is foundational. Self-hosted PTC platforms are prime targets for malicious actors due to the direct financial incentives. Our review scrutinizes several aspects:-
Input Validation and Sanitization: A common attack vector, particularly for PHP applications, is insufficient input validation. SQL injection (SQLi) and Cross-Site Scripting (XSS) vulnerabilities arise when user-supplied data is not properly validated, sanitized, and escaped before being used in database queries or rendered in HTML. Solid PTC must demonstrate robust practices here across all user-facing inputs, including administrative forms, advertiser campaign descriptions, and member profile fields. Without this, the platform is a prime target for data breaches and content defacement.
-
Authentication and Session Management: Secure password hashing (e.g., bcrypt, Argon2, not MD5/SHA1), multi-factor authentication (MFA) options, and secure session management (e.g., HTTPOnly cookies, token expiration, brute-force protection, account lockout mechanisms) are non-negotiable. Compromised credentials are a direct path to administrative takeover or account theft.
-
Access Control: Proper Role-Based Access Control (RBAC) ensures users can only access resources and perform actions appropriate to their role (admin, advertiser, member). Horizontal and vertical privilege escalation vulnerabilities, where a user can perform actions or access data beyond their authorized scope, are severe flaws that must be prevented through stringent server-side checks.
-
Payment Gateway Integration: The security of financial transactions relies heavily on secure integration with payment processors. This means avoiding direct handling of sensitive card data where possible (using tokenization services), implementing strong encryption (SSL/TLS) for all transactions, and adhering to PCI DSS compliance standards if card data is ever touched directly – though for most self-hosted scripts, relying on third-party gateways to handle the sensitive data is the safer, and more common, approach. Any custom payment module needs meticulous security auditing.
-
Protection Against Ad Fraud: Beyond general application security, PTC platforms face specific threats like bot traffic, click farms, and proxy networks. Effective anti-cheat mechanisms are crucial for maintaining advertiser trust and publisher legitimacy. These often involve IP analysis (blacklisting known VPNs/proxies, detecting anomalous IP changes), cookie tracking, browser fingerprinting, time-based click validation (e.g., minimum view duration, random click patterns), and robust CAPTCHA integrations. The sophistication and real-time nature of these mechanisms dictate the platform's long-term viability against financial fraud.
A self-hosted solution places the onus of server and application security squarely on the operator. This includes keeping the underlying operating system, web server, database, and PHP version patched and updated, as well as configuring firewalls and intrusion detection systems. The security of the application code itself, however, is the vendor's primary responsibility. Any critical review must consider the potential for unaddressed vulnerabilities in the shipped product, which can only be fully assessed through a professional code audit.
Performance and Scalability
A PPC platform can experience significant traffic spikes, especially if campaigns gain traction or an administrator launches a promotional event. Performance and scalability are thus key metrics for operational resilience and profitability.-
Database Optimization: High transaction volumes (clicks, impressions, user activity, payments) necessitate an optimized database schema, proper indexing on frequently queried columns, and efficient query design (avoiding N+1 queries, using joins effectively). Poorly written queries can cripple a system under moderate load, leading to timeouts and a degraded user experience. Database partitioning or sharding might be necessary for very large-scale operations, but this is rarely built into off-the-shelf scripts.
-
Caching Mechanisms: Implementing caching for frequently accessed but static or semi-static data (e.g., ad rotations, system settings, common pages) can significantly reduce database load and improve response times. This could involve opcode caches (OPcache for PHP bytecode), object caches (Redis, Memcached for database query results or rendered HTML fragments), or even browser-level caching for static assets (images, CSS, JavaScript).
-
Asynchronous Processing: Tasks like sending mass emails, generating complex, data-intensive reports, or processing large numbers of ad clicks can be resource-intensive and time-consuming. Offloading these to background jobs or message queues (e.g., using a cron job for batch processing, or more advanced queue systems like RabbitMQ or SQS) can prevent the main application from becoming unresponsive and blocking user requests.
-
Server Infrastructure: While the software itself provides the foundation, its ability to scale depends heavily on the underlying infrastructure. A well-designed platform should be able to leverage load balancing to distribute traffic across multiple web servers, database replication (master-slave or multi-master) for read scalability and redundancy, and potentially a Content Delivery Network (CDN) for serving static assets, allowing for horizontal scaling. However, many off-the-shelf scripts are not architected with this level of enterprise-grade scalability in mind, often requiring significant custom development and architectural changes to achieve it.
The "advanced" tag implies consideration for these aspects, but in many cases, commercial scripts prioritize features over robust, scalable architecture. A critical assessment will look for evidence of clean code, modularity, and adherence to modern development practices that facilitate performance tuning and scaling, rather than monolithic structures that become bottlenecks.
User Experience and Feature Set
Beyond the technical underpinnings, the practical usability of Solid PTC for its diverse audience—administrators, advertisers, and members—is paramount for its success and adoption.-
Administrator UX: An intuitive, well-organized admin panel reduces operational friction and the learning curve. Features like drag-and-drop campaign management, real-time analytics dashboards, granular user activity logs, and clear financial reporting are vital. The ease of setting up new ad types, managing payment processors, and configuring anti-cheat rules directly impacts an operator's efficiency and ability to react to market changes or threats.
-
Advertiser UX: Advertisers need clear campaign creation workflows, simple yet powerful budgeting tools, and transparent, easily digestible reporting. The ability to quickly launch, pause, and modify campaigns, alongside easy access to performance data and deposit options, will determine their satisfaction and continued investment in the platform. A confusing or slow advertiser experience will drive clients away.
-
Member UX: For publishers, a straightforward interface for viewing earnings, initiating withdrawals, and understanding referral programs is essential. Any friction here can lead to high churn rates. The availability of diverse ad formats, consistent payment processing, and transparent earning rules are key motivators for continued engagement. Gamification elements, if implemented, should be intuitive and genuinely rewarding.
-
Feature Breadth: Solid PTC should ideally offer a wide array of ad types (e.g., standard PPC, PTC (Paid to Click), PTR (Paid to Read), PTU (Paid to Upload), Banner Ads, Text Ads, Featured Ads, Login Ads, Video Ads, Traffic Exchange). The more options, the greater the flexibility for advertisers to promote their products and services, and the greater the potential for publisher earnings, which in turn fuels the ecosystem.
-
Monetization Flexibility: An "advanced" system often supports multiple revenue streams beyond simple click charges, such as premium memberships with enhanced features for both advertisers and publishers, advertising package sales, micro-tasks (surveys, offer walls), and perhaps even integrated affiliate marketing programs. The ability to configure these revenue models flexibly allows the operator to adapt to market demands.
The quality of the frontend design, responsiveness across devices, and the clarity of user flows significantly influence adoption and retention across all user types. A modern, clean, and responsive interface is not just a cosmetic feature but a critical functional component for user engagement and trust.
Strengths and Weaknesses of Self-Hosted PTC Platforms
**Strengths:**-
Full Control: The primary advantage is complete ownership and control over the platform, data, and business logic. This allows for specific customizations, branding, and integration with proprietary systems without vendor lock-in.
-
No Recurring SaaS Fees (for the software itself): Once purchased, the core software might not incur monthly fees, unlike SaaS alternatives, although hosting and maintenance costs remain a significant ongoing expense.
-
Potentially Higher Profit Margins: Without a third-party intermediary taking a cut of every transaction or managing advertiser/publisher relationships, the operator retains a larger share of the revenue, assuming efficient operation.
-
Data Sovereignty: All platform data resides on the operator's servers, which can be crucial for privacy regulations (e.g., GDPR), intellectual property concerns, and auditing requirements.
Weaknesses:
-
Operational Overhead: Running a self-hosted platform demands significant technical expertise for server management, security patching, application updates, database maintenance, and troubleshooting. This typically requires a dedicated technical team or skilled individual.
-
Initial Investment & Maintenance: While no SaaS fees, there's an upfront cost for the software itself, server infrastructure (hardware or cloud), and ongoing costs for security monitoring, regular backups, software updates, and potential developer support or custom development.
-
Security Responsibility: The operator bears the full burden of protecting against cyber threats (hacking, data breaches, DDoS attacks), a complex and evolving challenge that requires continuous vigilance and expertise.
-
Scalability Challenges: Without a well-architected solution or significant custom development, scaling to handle high traffic and transaction volumes can be problematic and costly, requiring expertise in infrastructure and database optimization.
-
Lack of Automatic Updates/Support: Unlike SaaS, updates often require manual intervention, testing, and deployment. Vendor support may be limited, time-gated, or require an additional subscription, placing a greater burden on the operator for problem resolution.
Solid PTC, like its counterparts, operates within this duality. Its "advanced" claims must be weighed against these inherent challenges. An operator considering such a platform must have a clear understanding of the technical resources available to them and a realistic assessment of the long-term commitment required.
Installation Guide: Deploying Solid PTC
Deploying a self-hosted platform like Solid PTC requires careful attention to detail and a foundational understanding of server administration. This guide assumes a basic familiarity with Linux command line, SSH, and database management. While specific steps might vary slightly depending on your hosting provider and exact server configuration, the core process remains consistent. For those exploring other self-hosted solutions, including [gplpal](https://gplapl.com/) offers a range of options, including various [Free download WordPress themes](https://gplpal.com/shop/), showcasing the breadth of self-deployable software available.1. Prerequisites: Server Environment
Before you even download Solid PTC, ensure your server meets the following minimum requirements. Attempting installation on an under-specced or incorrectly configured environment will invariably lead to instability, performance issues, or outright failure.-
Operating System: A modern Linux distribution (e.g., Ubuntu, CentOS, Debian).
-
Web Server: Apache (with mod_rewrite enabled and configured) or Nginx (with PHP-FPM configured).
-
PHP Version: PHP 7.4 or higher is the practical minimum. PHP 8.1 or 8.2 is preferred for performance and security, but you must ensure full compatibility of the Solid PTC script, as some older commercial scripts might exhibit issues with newer PHP versions without vendor updates.
-
Database: MySQL 5.7+ or MariaDB 10.2+. Ensure proper configuration for maximum connections and memory usage.
-
PHP Extensions: The following PHP extensions are typically mandatory:
-
mysqli (for MySQL database connectivity)
-
gd (for image manipulation, e.g., CAPTCHA generation, ad banner resizing)
-
curl (for external API calls, e.g., payment gateway integrations, fraud checks)
-
mbstring (for multi-byte string functions, crucial for internationalization)
-
json (for JSON encoding/decoding, common in API responses and data exchange)
-
openssl (for secure connections and cryptographic functions)
-
zip (for unpacking archives, potentially used by installer or update routines)
-
fileinfo (for robust detection of file types during uploads)
-
xml (for XML parsing, if any integrations use XML-based APIs)
-
pdo and pdo_mysql (often required even if mysqli is primary, for broader compatibility)
-
allow_url_fopen (often required for certain external resource fetches, though curl is generally preferred for security reasons and should be prioritized)
-
PHP Configuration:
-
memory_limit: At least 256MB, preferably 512MB or more for demanding operations or larger datasets.
-
max_execution_time: At least 120 seconds. Some bulk operations or complex reports might require more.
-
post_max_size and upload_max_filesize: Ensure these are sufficient for ad banner uploads and other user-submitted content.
-
Storage: Sufficient disk space for the application files, the ever-growing database, and user-uploaded content (ad banners, log files, cache). Factor in projected growth.
-
SSL Certificate: Absolutely essential. Install a valid SSL certificate (e.g., free from Let's Encrypt via Certbot) and configure your web server to force HTTPS for all traffic. Operating a financial platform without HTTPS is negligent.
Verification (Linux Command Line Example):
Check PHP version
php -v
Check MySQL/MariaDB client version (login to MySQL/MariaDB client to check server version)
mysql -V
Check PHP extensions (replace 'gd' with desired extension)
php -m | grep gd
To check PHP configuration limits (grep for relevant settings)
php -i | grep "memory_limit" php -i | grep "max_execution_time"
2. Database Setup
You need to create a dedicated database and a user with specific privileges for Solid PTC. This is a fundamental security practice, limiting the scope of database access should the web application be compromised.- Access MySQL/MariaDB: Log in to your database server as a root user or a user with sufficient privileges to create databases and users.
mysql -u root -p
Enter your root password when prompted.- Create Database: Choose a descriptive and unique name for your database, e.g., solidptc_db. It is crucial to use utf8mb4 character set and collation for broad character support, including emojis, which can prevent data corruption.
CREATE DATABASE solidptc_db CHARACTER SET utf8mb4 COLLATE utf8mb4_unicode_ci;
- Create User and Grant Privileges: Create a new user (e.g., solidptc_user) and assign a strong, unique password. Grant this user full privileges ONLY on the newly created database. Limiting privileges is a key security measure.
CREATE USER 'solidptc_user'@'localhost' IDENTIFIED BY 'YOUR_VERY_STRONG_PASSWORD'; GRANT ALL PRIVILEGES ON solidptc_db.* TO 'solidptc_user'@'localhost'; FLUSH PRIVILEGES;
**Important:** Replace 'YOUR_VERY_STRONG_PASSWORD' with a unique, complex password that is difficult to guess. If your web server and database server are on different machines, replace 'localhost' with the web server's IP address or hostname. If you're using a hosted database service, follow their instructions for user creation and IP whitelisting.- Exit MySQL:
EXIT;
3. Uploading Files
After downloading the Solid PTC archive (typically a .zip file), you'll need to upload its contents to your web server's document root or a sub-directory, depending on where you want the application to be accessible.-
Extract the Archive: Unzip the downloaded Solid PTC package on your local machine. You should find a main directory containing all the application files and sub-folders.
-
Connect via FTP/SFTP: Use an FTP client (like FileZilla) or SFTP (SSH File Transfer Protocol) to connect securely to your web server. SFTP is strongly preferred due to its encrypted nature.
-
Upload Files: Upload the entire contents (all files and folders) of the extracted Solid PTC package to your desired location on the server.
-
If you want Solid PTC to be accessible directly at your domain (e.g., https://yourdomain.com/), upload all contents into your web server's document root (e.g., /var/www/html/ for Apache on Linux, or the specific root configured in Nginx).
-
If you want it accessible via a sub-directory (e.g., https://yourdomain.com/ptc/), create a directory (e.g., ptc) within your document root and upload the files there.
-
Set File Permissions: This is a critical security and functional step. Incorrect permissions can lead to vulnerabilities (e.g., unauthorized file modification) or prevent the application from functioning (e.g., inability to write cache files or upload images).
Navigate to your Solid PTC root directory (adjust path as needed)
cd /var/www/html/solidptc/
Set all directories to 755 (read, write, execute for owner; read, execute for group/others)
find . -type d -exec chmod 755 {} \;
Set all files to 644 (read, write for owner; read for group/others)
find . -type f -exec chmod 644 {} \;
Identify specific directories that require write permissions for the web server user
(e.g., cache, uploads, logs, templates_c). These typically need 775 or 777 (less secure)
You MUST consult Solid PTC's official documentation for exact directories.
Example for common writable directories (adjust names and paths as needed):
chmod -R 775 cache/ chmod -R 775 uploads/ chmod -R 775 logs/ chmod -R 775 templates_c/ # if Smarty or similar templating engine is used
**Warning:** Be extremely cautious with chmod 777. Use it only if absolutely necessary and only for specific directories. If 777 is used, ideally, change it back to a more restrictive permission (e.g., 775, ensuring the web server user is in the correct group) after installation or when files are no longer being written to by the application. Always prioritize the principle of least privilege.4. Configuration File Setup
The Solid PTC script will have a main configuration file, typically named something like config.php, settings.php, or located in a dedicated directory like app/config/. This file holds crucial database credentials and other core system settings.-
Locate and Rename: Find a file named config-sample.php or similar (sometimes it's just config.php directly). If it's a sample, rename it to the correct configuration filename (e.g., config.php). If you downloaded the script from a reliable source, it might be pre-named correctly.
-
Edit the Configuration File: Open this file using a text editor (via SSH, e.g., nano config.php, or by downloading, editing locally, and re-uploading via SFTP).
You'll need to locate the database connection parameters and update them with the details you created in Step 2:
// Database Settings define('DB_HOST', 'localhost'); // Database host (usually 'localhost' unless separate server) define('DB_USER', 'solidptc_user'); // Database user define('DB_PASS', 'YOUR_VERY_STRONG_PASSWORD'); // Database user's password define('DB_NAME', 'solidptc_db'); // Database name
// Other settings like site URL, admin email, default timezones, etc., might also be present. // Update these as necessary to match your environment.
**Security Note:** Ensure this configuration file is not directly accessible via a web browser. Modern frameworks often place configuration outside the web root. If it's within the web root, ensure your web server configuration (e.g., .htaccess for Apache) denies direct access to .php files in config directories, or specifically to the config file itself. Restrictive file permissions (e.g., 600 or 640) for this file are also recommended if possible without breaking the application.5. Running the Installation Script
Most self-hosted applications provide an installer wizard to set up the database tables, populate initial data, and perform other first-time configurations.-
Access the Installer: Open your web browser and navigate to the Solid PTC installation URL. This is typically:
-
https://yourdomain.com/install/
-
https://yourdomain.com/setup/
-
https://yourdomain.com/solidptc/install/ (if installed in a sub-directory)
Consult the official Solid PTC documentation for the precise installation path. If you encounter a "404 Not Found" error, double-check the path and ensure web server rewrites are working. -
Follow On-Screen Instructions: The wizard will guide you through several steps:
-
License Agreement: Read and accept the software's license terms.
-
System Requirements Check: The installer should verify that your server meets all prerequisites (PHP version, extensions, permissions). Address any warnings or errors before proceeding; do not ignore them.
-
Database Import: It will use the credentials from your config.php to connect to the database and import the necessary tables and initial data. This step is crucial for the application's functionality.
-
Administrator Account Creation: You will be prompted to create your primary administrator username and password. Choose a very strong, unique password (e.g., 16+ characters, mixed case, numbers, symbols). Do not use "admin" as a username.
-
Site Settings: Basic site name, main URL, contact email, and perhaps default currency or language.
-
Complete Installation: Once all steps are complete, the installer will confirm successful installation and usually provide a link to the admin panel.
6. Post-Installation Security and Configuration
These steps are critical for securing your new platform, ensuring optimal operation, and maintaining its integrity over time. Neglecting these can lead to serious vulnerabilities or functional issues.- Delete or Secure the Installer Directory: Immediately delete the install/ or setup/ directory from your server. Leaving it exposed is a major security vulnerability that attackers can exploit to re-run the installation or gain unauthorized access. If deletion isn't feasible (e.g., for future upgrades, though this is poor design), at least secure it with strong .htaccess rules or deny web access via your web server configuration.
Example: Delete installer directory via SSH
rm -rf /var/www/html/solidptc/install/
-
Change Default Admin Credentials: Even if you set them during installation, verify that no default "admin/password" accounts remain. Check for any hardcoded default accounts or easy-to-guess usernames.
-
Configure Cron Jobs: Solid PTC will rely heavily on scheduled cron jobs for automated tasks. These are essential for the platform's functionality and economic model. Examples include:
-
Processing clicks and impressions to update balances.
-
Running anti-cheat routines to detect and mitigate fraud.
-
Sending daily reports, newsletters, or notifications.
-
Processing automated payouts to members.
-
Maintaining database integrity and clearing old logs/cache.
Access your server's cron tab (crontab -e via SSH) and add the necessary entries. The Solid PTC documentation will provide the exact commands and frequency recommendations. **Example Cron Entry (adjust path to PHP binary and script locations):**
Run main processing script every minute to handle clicks, etc.
-
-
-
-
- /usr/bin/php /var/www/html/solidptc/cron.php >/dev/null 2>&1
-
-
-
Run daily maintenance script at 3 AM server time
0 3 * * * /usr/bin/php /var/www/html/solidptc/daily_maintenance.php >/dev/null 2>&1
Ensure the PHP path is correct (e.g., /usr/bin/php, /usr/local/bin/php, or a specific PHP version path like /usr/bin/php7.4). Use the full path for robust execution.-
Review and Harden Web Server Configuration:
-
Apache: Ensure .htaccess files are being processed (AllowOverride All in your virtual host configuration). Configure robust security headers (e.g., Content-Security-Policy, X-Frame-Options, X-Content-Type-Options, Referrer-Policy) via your main Apache config or .htaccess. Disable directory listing (Options -Indexes).
-
Nginx: Implement similar security headers and ensure proper fastCGI configuration for PHP processing, including preventing direct access to PHP files outside the main index.
-
HTTPS Redirection: Ensure all HTTP traffic is permanently redirected to HTTPS.
-
Configure Email Settings: Set up SMTP details (host, port, username, password) for reliable email delivery (password resets, registration confirmations, notifications, mass emails). Using an authenticated SMTP service (e.g., SendGrid, Mailgun) is far more reliable than local sendmail.
-
Backup Strategy: Implement a robust, automated backup strategy for both your database (daily full backups, possibly more frequent incremental backups) and your Solid PTC application files. Store backups off-site and test the restoration process periodically.
-
Regular Updates and Monitoring: Subscribe to Solid PTC's official updates or community forums. Apply security patches and version upgrades promptly. Set up server monitoring (CPU, memory, disk I/O, network traffic) and application error logging.
Troubleshooting Common Installation Issues
-
"500 Internal Server Error": This generic error usually points to incorrect file permissions, an error in .htaccess (for Apache), or a critical PHP configuration issue (e.g., missing extension, memory limit exceeded). Check your web server error logs (Apache: /var/log/apache2/error.log; Nginx: /var/log/nginx/error.log) and PHP error logs for specifics.
-
Blank Page: Often caused by PHP errors that are suppressed from displaying. Enable PHP error reporting temporarily during debugging by adding display_errors = On and error_reporting = E_ALL to your php.ini, or by adding ini_set('display_errors', 1); error_reporting(E_ALL); at the top of your main application index file. Remember to disable this in production.
-
Database Connection Errors: Double-check your config.php for correct database name, username, password, and host. Verify the MySQL user has privileges on the correct database and that the MySQL server is running and accessible from the web server.
-
"Page Not Found" / Rewrite Issues: Ensure mod_rewrite is enabled for Apache and configured correctly in your virtual host or .htaccess. For Nginx, ensure your location / block includes a try_files directive that routes requests to your main PHP index file (e.g., index.php?$query_string).
-
PHP Extension Missing: The installer or application will typically throw a clear error or warning if a required PHP extension is missing. Install the missing extension (e.g., sudo apt install php7.4-gd on Ubuntu/Debian, or sudo yum install php-gd on CentOS/RHEL).
-
Permission Denied Errors: Review the file permissions for the directories that require write access (e.g., cache, uploads, logs). Ensure the web server user (e.g., www-data for Apache/Nginx on Ubuntu, apache or nginx for CentOS) has write permissions to these directories.
Conclusion: The Practicality of Solid PTC
Solid PTC presents itself as an "Advanced Pay Per Click Platform," and for a specific subset of operators, it may indeed offer the direct control and customization sought after. Its utility is highest for those who possess the technical acumen to manage a self-hosted environment, understand the nuances of server and application security, and are prepared for the operational demands such a system entails. The robust feature set, particularly for managing diverse ad types, anti-cheat mechanisms, and user roles, forms a solid foundation for building a niche advertising network.
However, the "advanced" designation also carries an expectation of enterprise-grade security, scalability, and performance architecture that often goes beyond what a single commercial script can deliver out-of-the-box without significant additional investment in infrastructure and expertise. Without direct access to the source code for a full audit, we emphasize that the onus falls heavily on the operator to implement rigorous security practices at the server level, to regularly monitor the application for vulnerabilities, and to maintain a vigilant watch over potential ad fraud. The initial setup, as detailed in the installation guide, is non-trivial and requires a competent administrator with hands-on server experience.
For entities prioritizing absolute control, data sovereignty, and a potentially higher profit margin by circumventing recurring SaaS fees, Solid PTC offers a viable, albeit demanding, path. For those lacking dedicated technical resources, or seeking a "set-it-and-forget-it" solution, a self-hosted platform like this will inevitably introduce significant operational overhead and potential risks. Its real value is realized not just in its feature list, but in the operational expertise brought to its deployment and ongoing management. Ultimately, the success of a Solid PTC deployment hinges as much on the administrator's capabilities and commitment as it does on the software's inherent quality and feature set.
评论 0